Hybrid Cryptography Model based on Authentication, Integrity & Privacy: Kapoor, Vivek, Bhat, Saurabh: 9786202010085: Amazon.com: Books

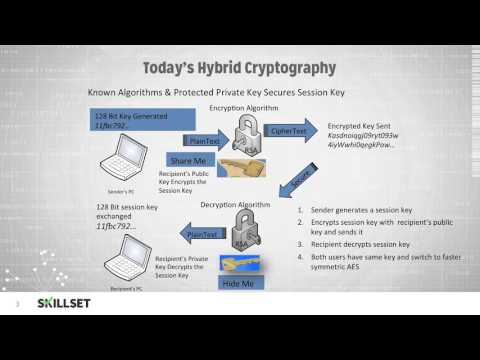
Figure 1 from Hybrid cryptography mechanism for securing self-organized wireless networks | Semantic Scholar

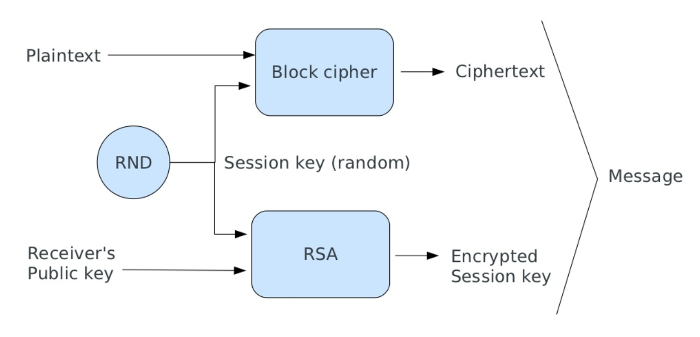
Hybrid encryption algorithm using Krishna and AES algorithms Figure 4,... | Download Scientific Diagram
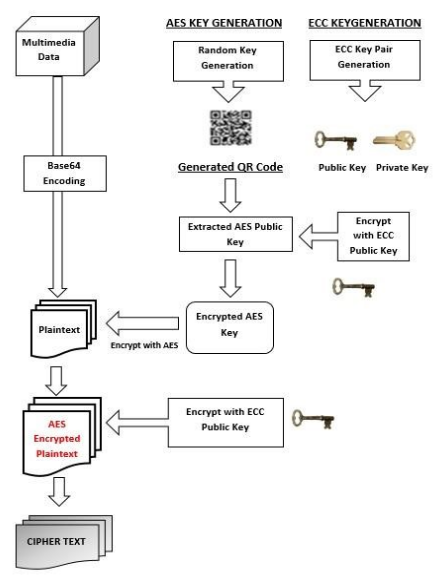
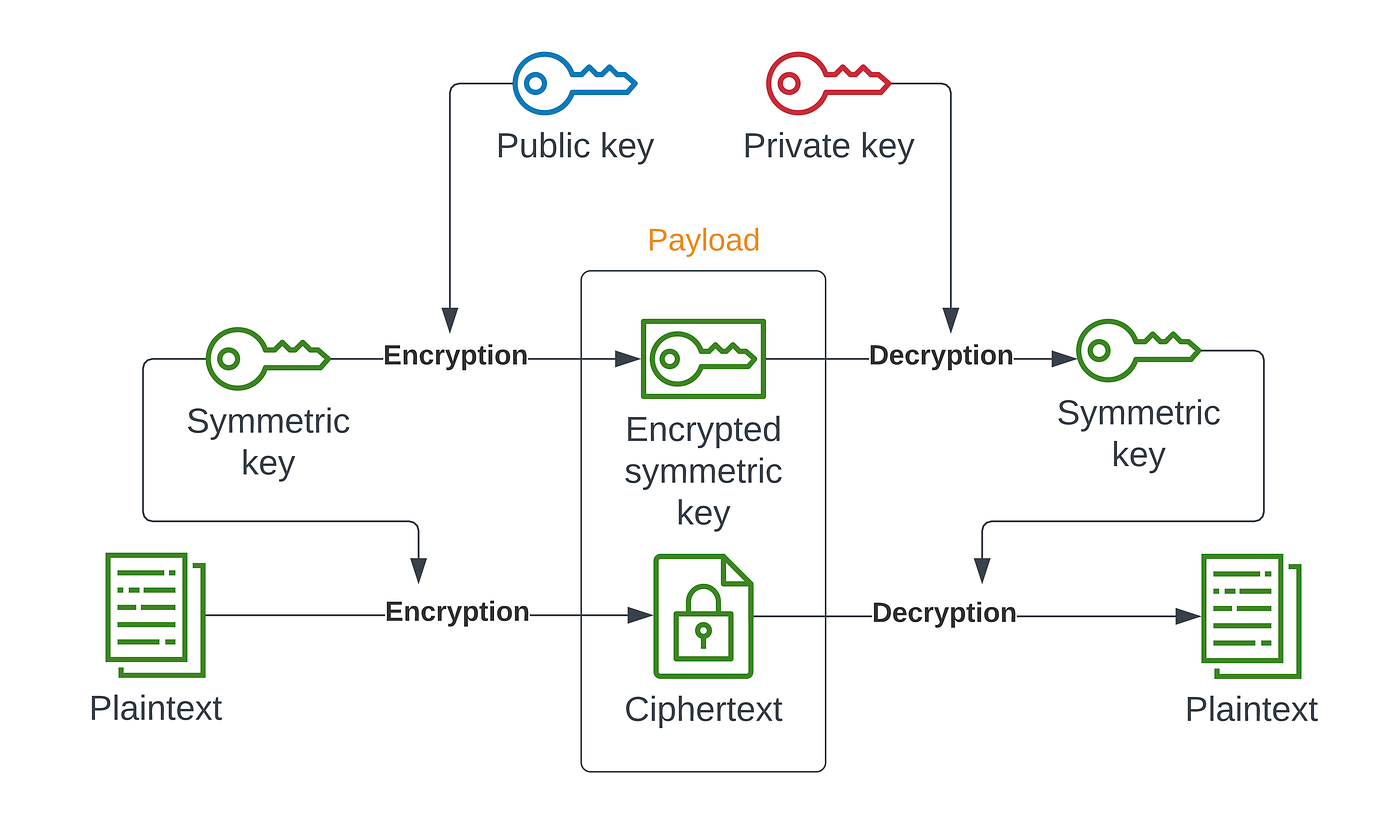
Hybrid-Cryptography | Implementation of a system capable of encryption and decryption of multimedia data (Text, Images, Videos, Audio etc.) using a hybrid model based on the amalgamation of symmetric encryption techniques such

A Comparative Study of Various Traditional and Hybrid Cryptography Algorithm Models for Data Security | SpringerLink
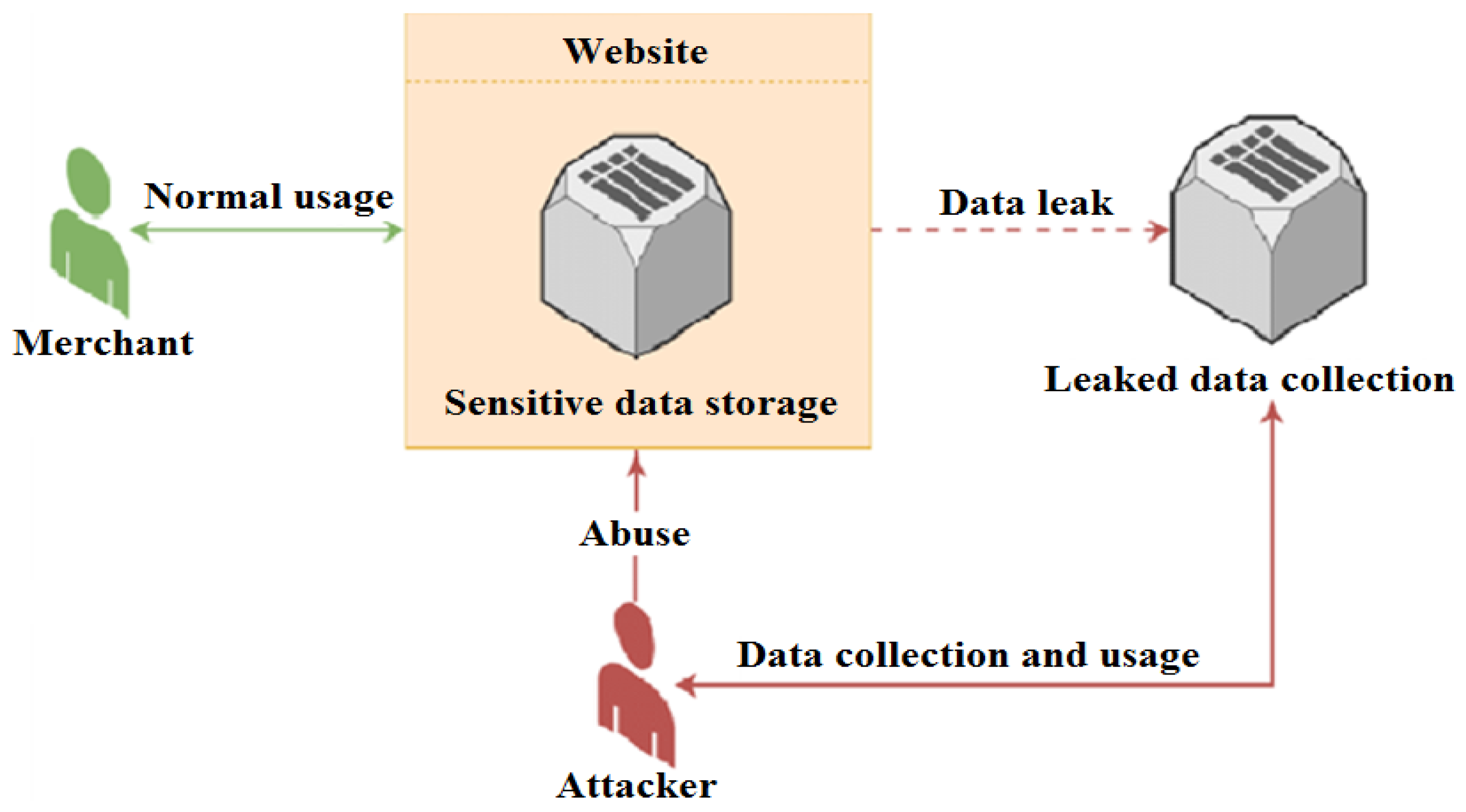
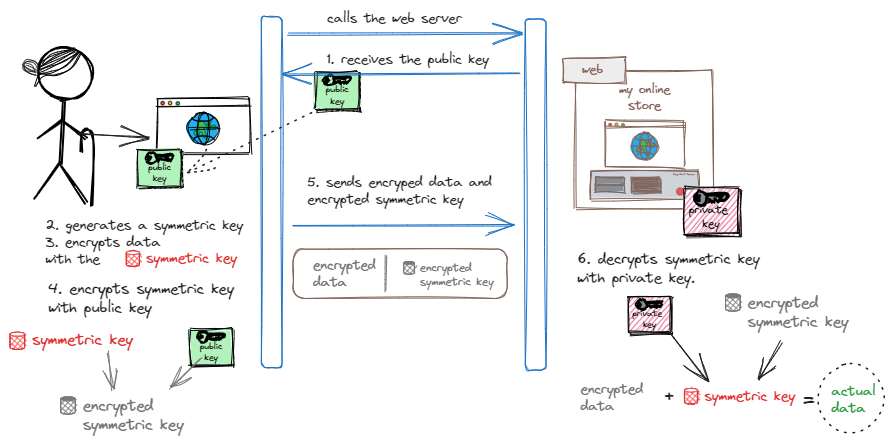
Future Internet | Free Full-Text | Applying Detection Leakage on Hybrid Cryptography to Secure Transaction Information in E-Commerce Apps